Integrating SIEM and IAM: A Technical Playbook for Unified Threat Detection
A practical technical guide on integrating SIEM and IAM platforms to break down data silos and enable unified threat detection across identity and security event data.
Executive Summary
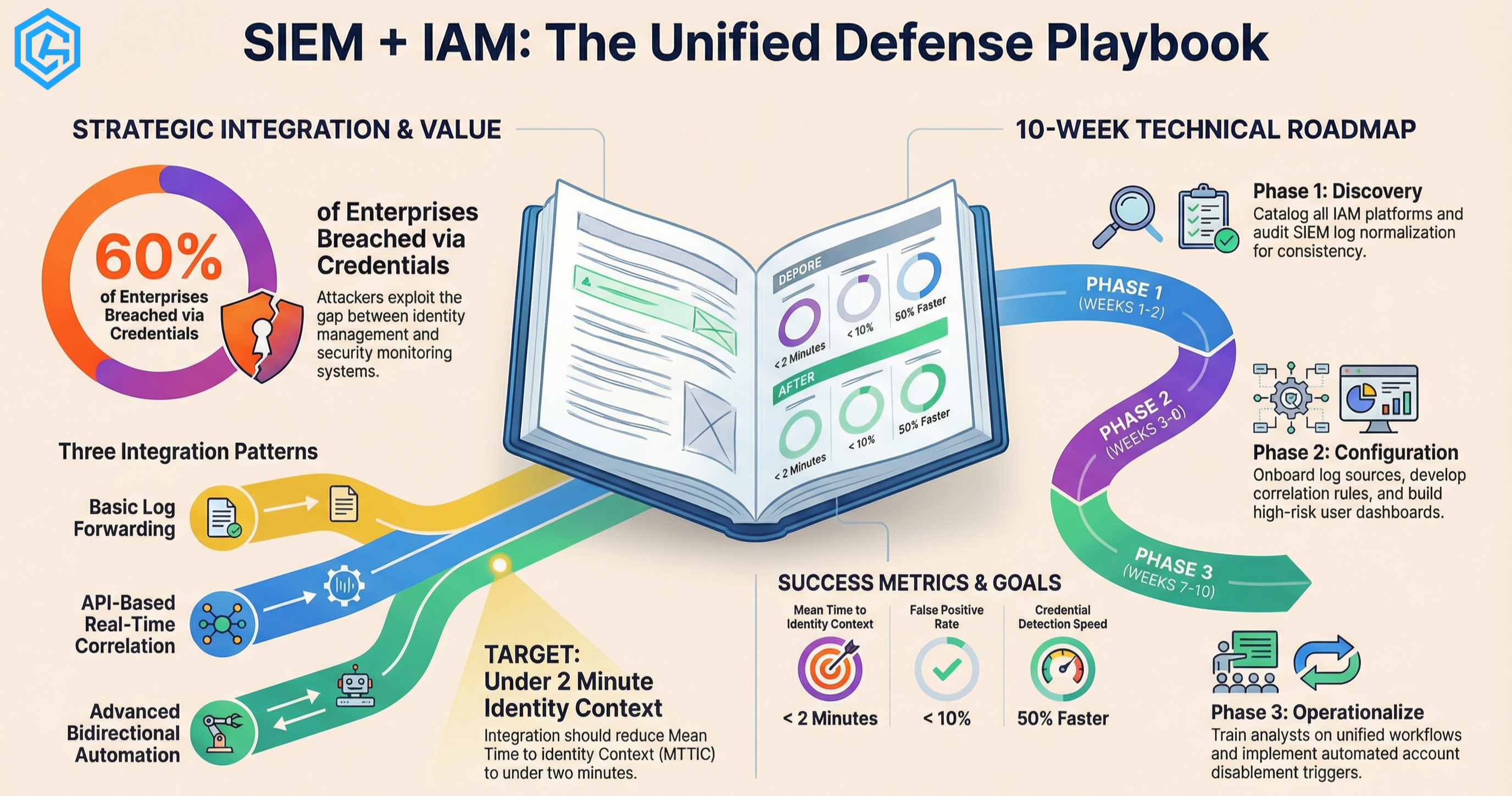
Security operations centers face a persistent blind spot: threat detection and identity management operate in separate silos. Your SIEM monitors logs, network traffic, and endpoint events. Your IAM platform manages user identities, privileges, and access policies. When these systems do not communicate, critical attack signals get missed.
This playbook provides a technical roadmap for integrating SIEM and IAM platforms. You will learn how to correlate identity events with security telemetry, reduce false positives, and detect compromised credentials before damage occurs. Whether you run QRadar with CyberArk, Splunk with Okta, or ArcSight with SailPoint, the principles remain consistent.
Why Integration Matters
The Identity Blind Spot in Threat Detection
Traditional SIEM implementations focus on network and endpoint telemetry. They answer questions like:
- Which IP addresses communicated?
- What files were accessed?
- Which processes executed?
But they often miss the identity context: Who initiated these actions? Were their credentials legitimate? Had their privileges escalated unusually?
Attackers exploit this gap. Compromised credentials now account for over 60% of initial access vectors in enterprise breaches. When a legitimate user account performs malicious actions, SIEM alerts without IAM context look like normal activity.
The SOC Analyst Problem
Without integration, analysts face a fragmented investigation workflow:
- SIEM triggers an alert on suspicious file access
- Analyst manually queries IAM platform for user context
- Switches between consoles to review privilege history
- Manually correlates timestamps across systems
- Decides whether to escalate based on incomplete data
Each context switch adds minutes. Hours pass before analysts understand the full picture. Attackers move faster.
Integration Architecture: Core Components
Data Sources You Need
From SIEM:
- Authentication logs (success/failure events)
- Privilege escalation attempts
- File and resource access events
- Network traffic flows
- Endpoint process execution
From IAM:
- User provisioning and deprovisioning events
- Role and entitlement changes
- Session start/end times
- Anomalous login patterns (geographic, time-based, device)
- Privileged access sessions
Integration Patterns
Pattern 1: Log Forwarding (Basic)
IAM platforms forward event logs to SIEM for centralized correlation.
Implementation:
- Configure IAM platforms (Okta, CyberArk, SailPoint) to send syslog or CEF formatted logs
- Parse and normalize IAM events within SIEM ingestion pipelines
- Create correlation rules matching identity events to security telemetry
Pros: Simple to implement, leverages existing SIEM infrastructure Cons: Delayed correlation (batch forwarding), potential log volume spikes
Pattern 2: API-Based Real-Time Correlation
SIEM queries IAM APIs for contextual enrichment during alert processing.
Implementation:
- Use IAM platform REST APIs (Okta System Log API, CyberArk Central Policy Manager API)
- Configure SIEM custom parsers or enrichment plugins
- Enable real-time lookups when alerts trigger
Pros: Real-time context, reduces false positives Cons: API rate limits require careful management, adds latency to alert processing
Pattern 3: Bidirectional Integration (Advanced)
SIEM and IAM platforms exchange threat intelligence and automatically trigger protective actions.
Implementation:
- SIEM detects compromised credentials → automatically notifies IAM to disable account
- IAM identifies high-risk user behavior → sends risk score to SIEM for elevated monitoring
- Use SOAR platforms (ServiceNow, Palo Alto XSOAR) to orchestrate workflows
Pros: Automated response, proactive threat containment Cons: Complex implementation, requires mature security operations
Platform-Specific Integration Guides
QRadar + CyberArk Integration
QRadar specializes in enterprise-grade correlation. CyberArk manages privileged access. Together, they create a powerful defense against credential-based attacks.
Data Flow Configuration:
-
Enable CyberArk PTA (Privileged Threat Analytics)
- Configure PTA to send risk scoring events via syslog
- Set severity thresholds for automated QRadar alerts
-
Configure QRadar DSM (Device Support Module)
- Install CyberArk DSM from IBM X-Force App Exchange
- Map CyberArk event categories to QRadar offense types
-
Build Custom Rules
- Create rules correlating CyberArk high-risk session alerts with QRadar authentication failures
- Flag sessions where CyberArk risk score exceeds threshold AND QRadar detects lateral movement
Key Events to Monitor:
PTA_VAULT_ALERT— High-risk privileged access detectedPSM_CONNECT— Privileged session monitoring connection eventsPTA_SUSPECTED_CREDENTIAL_THEFT— Potential credential compromise indicators
Splunk + Okta Integration
Splunk excels at data lake analytics. Okta provides cloud-native identity. Their integration works well for hybrid cloud environments.
Implementation Steps:
-
Install Splunk Add-on for Okta
- Available on Splunkbase
- Provides prebuilt field extractions and CIM compliance
-
Configure Okta System Log Streaming
- Enable Okta System Log API access
- Configure Splunk HTTP Event Collector (HEC) or use modular input
-
Build Correlation Searches
- Detect impossible travel: Okta geolocation data + Splunk VPN logs
- Identify privilege abuse: Okta group changes preceding suspicious file access
Sample SPL Query:
index=okta sourcetype=okta:im2 severity=WARN
| lookup user_risk_scores user
| where risk_score > 70
| join user
[search index=firewall sourcetype=pan:traffic action=allow
| stats count by user, dest_ip]
| where count > 10
| table user, risk_score, dest_ip, count
ArcSight + SailPoint Integration
ArcSight provides mature correlation for regulated industries. SailPoint handles identity governance at scale. This pairing suits enterprises with complex compliance requirements.
Connector Configuration:
-
Deploy SailPoint SecurityIQ Integration
- Enables SailPoint to share access certification campaign data
- Feeds entitlement visibility into ArcSight correlation
-
Map Identity Context to CEF
- SailPoint generates CEF-formatted events for ArcSight ingestion
- Includes user lifecycle events, access reviews, policy violations
-
Create ArcSight Active Lists
- Dynamically populate lists of high-risk users from SailPoint policy scans
- Use lists in real-time correlation rules for elevated monitoring
Technical Implementation Roadmap
Phase 1: Discovery and Baseline (Weeks 1-2)
Identity Data Audit:
- Catalog all IAM platforms in use (often multiple: AD, Okta, CyberArk, legacy)
- Map user directories and authentication flows
- Identify shadow IAM (SaaS apps managed outside central IT)
SIEM Log Review:
- Verify current authentication event ingestion
- Check field normalization quality (are user identifiers consistent?)
- Assess retention policies (do logs cover long-dwell attacks?)
Correlation Gap Analysis:
- List questions your SOC cannot answer today
- Prioritize gaps by attack scenario likelihood
- Document business impact of each gap
Phase 2: Configure Integrations (Weeks 3-6)
Log Source Onboarding:
- Configure IAM platforms to forward security-relevant events
- Implement parsing and normalization rules
- Validate field mapping (user IDs, timestamps, event types)
Correlation Rule Development:
- Start with high-confidence, low-noise rules
- Test against historical incidents if available
- Tune thresholds based on false positive rates
Dashboard Creation:
- Unified identity and security timeline
- High-risk user monitoring views
- Privileged access anomaly detection
Phase 3: Operationalize (Weeks 7-10)
SOC Training:
- Train analysts on unified investigation workflows
- Document runbooks for common identity-based alerts
- Establish escalation paths for high-risk identity events
Continuous Tuning:
- Review alert quality weekly
- Adjust correlation thresholds based on operational feedback
- Expand integration scope as maturity grows
Response Automation:
- Implement account disablement for confirmed compromises
- Automate privilege review triggers based on risk scores
- Build feedback loops between SIEM detections and IAM policies
Common Pitfalls and How to Avoid Them
Pitfall 1: Log Volume Explosion
IAM platforms generate massive event volumes. Unfiltered ingestion overwhelms SIEM licensing and performance.
Solution: Implement aggressive filtering at the source. Forward only security-relevant events:
- Authentication success/failure
- Privilege changes
- Anomalous behavior alerts
- Session anomalies
Drop routine provisioning, self-service password resets, and non-security events.
Pitfall 2: User Identity Sprawl
One person has multiple identifiers: AD username, Okta ID, CyberArk account, email address. Correlation breaks without normalization.
Solution: Implement identity correlation tables in your SIEM. Create lookup mechanisms mapping all identifiers to a master user record. Validate during Phase 1 discovery.
Pitfall 3: Stale Identity Data
Terminated employees remain in IAM systems. Access certifications lag behind actual role changes. SIEM correlates against outdated identity context.
Solution: Establish automated deprovisioning workflows. Use SIEM to audit IAM data freshness (alert on old last-logon dates with active accounts). Cross-reference HR termination feeds.
Pitfall 4: Alert Fatigue from Identity Noise
IAM generates legitimate anomalies (traveling users, new device registrations). SIEM correlation without business context creates false positives.
Solution: Seed SIEM with business context: user locations, expected working hours, approved devices. Correlate IAM anomalies against business rules before alerting.
Measuring Success
Operational Metrics
- Mean Time to Identity Context (MTTIC): Time from alert to full user context understanding. Target: under 2 minutes.
- False Positive Rate: Identity-related alerts that resolve as legitimate activity. Target: under 10%.
- Investigation Depth: Percentage of incidents where analysts retrieved IAM context. Target: 100% for credential-related alerts.
Security Outcomes
- Credential Compromise Detection Time: Hours from initial credential theft to detection. Integration should reduce this by 50%+.
- Lateral Movement Prevention: Number of attacks stopped before privilege escalation.
- Identity Policy Effectiveness: Reduction in risky access patterns discovered during investigations.
Conclusion
SIEM and IAM integration transforms security operations from reactive log analysis into proactive threat detection. By correlating identity context with security events, you close the gap attackers exploit most: compromised credentials.
Start with log forwarding from your primary IAM platform to your SIEM. Build correlation rules around high-confidence scenarios: impossible travel, privilege escalation anomalies, and disabled accounts exhibiting activity. Expand to API-based enrichment and bidirectional response as your team matures.
The platforms supported — QRadar, Splunk, ArcSight, CyberArk, Okta, SailPoint — provide the technical foundation. Implementation success depends on clean data, consistent user identification, and analyst training. With those elements in place, unified threat detection becomes a force multiplier for your security operations.
For organizations lacking the in-house expertise to implement these integrations, specialized consulting and managed security services accelerate deployment and ensure best-practice configuration from day one.
At Cyberaube, we implement and operate integrated SIEM-IAM architectures for enterprises across India. Our certified specialists handle platform configuration, custom correlation rule development, and SOC workflow optimization. Whether you need help integrating QRadar with CyberArk, Splunk with Okta, or any other combination, we can help.
Discuss SIEM-IAM integration with our team
SIEM and IAM Implementation Services
Cyberaube Technologies delivers end-to-end SIEM and IAM implementation services — from architecture design to production deployment and ongoing managed support. Our certified specialists have integrated QRadar with CyberArk, Splunk with Okta, and 15+ other platform combinations across Indian enterprises.
Explore our professional services or speak to our integration team.
About the Author
Saurabh Pande is Co Founder of Cyberaube Technologies with 10+ years of hands on experience implementing integrated security stacks, including SIEM-IAM architectures, for organizations across BFSI, healthcare, and technology sectors.
About Cyberaube
Cyberaube provides cybersecurity staffing, 24/7 managed security services, and expert consulting for SIEM, IAM, and data protection platforms. Our certified specialists implement and operate QRadar, Splunk, ArcSight, CyberArk, Okta, SailPoint, and integrated security stacks for enterprises across India and globally.
Need help integrating your SIEM and IAM platforms? Our implementation teams specialize in cross-platform correlation architecture, custom rule development, and SOC workflow optimization. Contact us to discuss your integration roadmap.