SEBI CSCRF Compliance Playbook for Indian BFSI Organizations
A practical guide to understanding, prioritizing, and implementing the Securities and Exchange Board of India's Cybersecurity and Cyber Resilience Framework — without the regulatory jargon.
Executive Summary
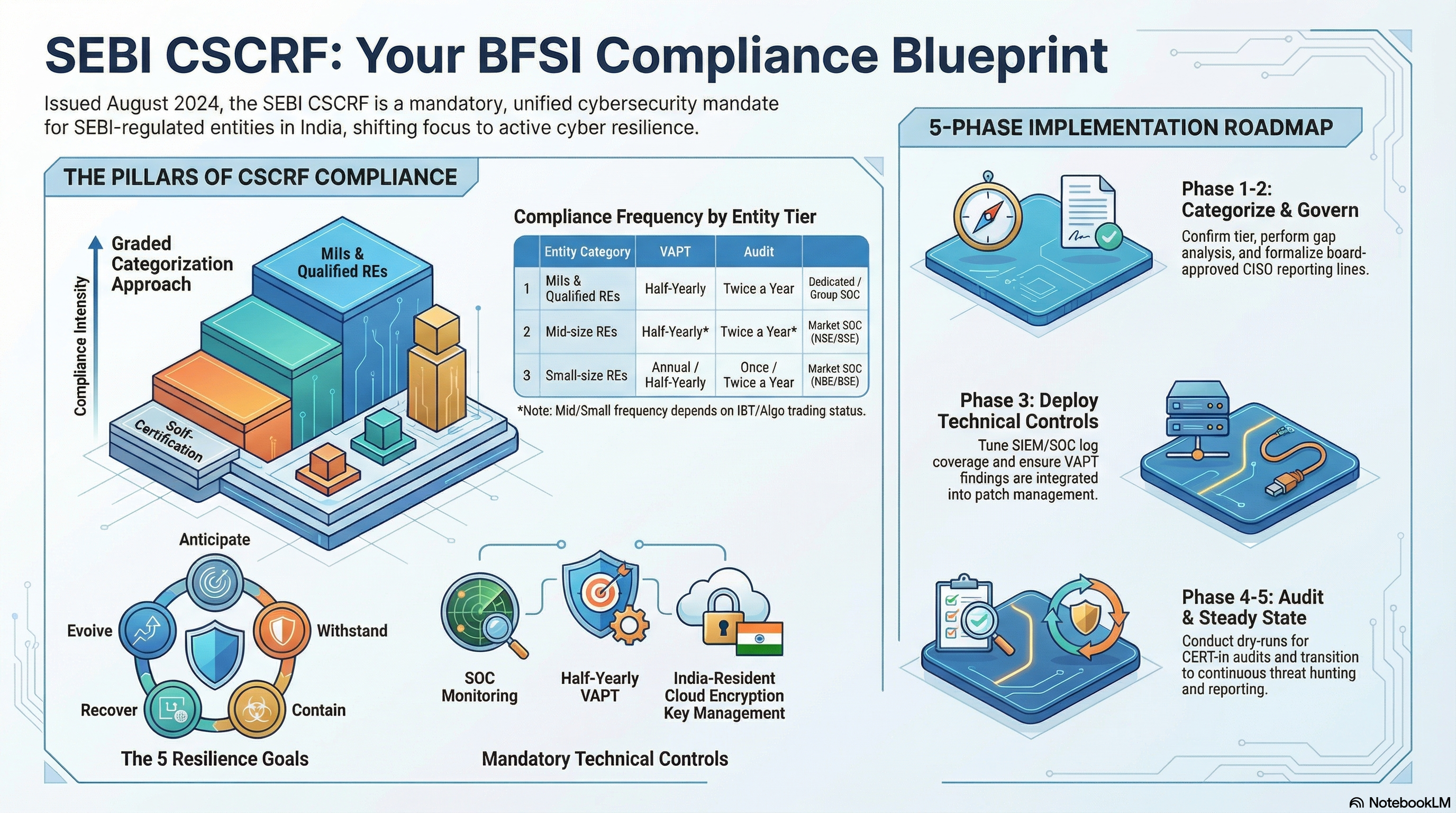
India's financial sector is under more regulatory scrutiny on cybersecurity than at any point in its history. The Securities and Exchange Board of India issued the Cybersecurity and Cyber Resilience Framework (CSCRF) in August 2024 — a comprehensive, standards-based mandate that supersedes every prior SEBI cybersecurity circular. For stock brokers, mutual funds, depositories, AMCs, portfolio managers, and other regulated entities, CSCRF is not an advisory. It is a compliance obligation with audit requirements, mandatory reporting, and enforcement consequences.
The challenge most organizations face is not awareness — it is translation. CSCRF runs to hundreds of pages across the main circular, two major clarification circulars, a 76-question FAQ, and technical addenda. CISOs and compliance leads are left to figure out what it means in practice: which controls are mandatory for their entity category, what their audit obligations are, and where the gaps in their current setup actually are.
This guide is a practitioner's playbook. It breaks down the framework by entity category, maps the real compliance requirements, identifies where most BFSI organizations are falling short, and gives you a structured roadmap to close the gaps — whether you are building controls from scratch or preparing for your first CSCRF audit cycle.
What is SEBI CSCRF?
The Cybersecurity and Cyber Resilience Framework was issued by SEBI on August 20, 2024, via circular SEBI/HO/ITD-1/ITD_CSC_EXT/P/CIR/2024/113. It replaces all previously issued SEBI cybersecurity guidelines, advisories, and circulars under a single unified framework.
CSCRF was developed in consultation with Market Infrastructure Institutions (MIIs), regulated entities, CERT-In, and SEBI's own High Powered Steering Committee on Cybersecurity. It draws from internationally recognized frameworks including ISO 27001, NIST 800-53, CIS v8, and BIS/CPMI-IOSCO guidelines — but adapts them for the specific risk profile of India's capital markets.
The core objective is twofold: protect the integrity of market operations from cyber threats, and ensure that entities can recover from incidents, not just defend against them.
The Five Cyber Resilience Goals
CSCRF builds on five cyber resilience goals, forming the spine of the entire framework:
| Goal | What It Means in Practice |
|---|---|
| Anticipate | Proactively identify threats and vulnerabilities before they are exploited |
| Withstand | Maintain critical operations under active attack |
| Contain | Limit the blast radius of a security incident |
| Recover | Restore normal operations quickly and completely |
| Evolve | Continuously improve posture based on threats, audits, and incidents |
These goals map to six security functions: Governance, Identify, Protect, Detect, Respond, and Recover — structures that practitioners familiar with NIST CSF will recognize, but with tighter mandates and India-specific requirements layered on top.
Who Does CSCRF Apply To?
CSCRF is applicable to all SEBI-regulated entities (REs). The framework adopts a graded approach, categorizing entities into five tiers based on their operational scale, asset size, client base, trading volume, and systemic importance:
| Category | Who It Covers | Compliance Intensity |
|---|---|---|
| Market Infrastructure Institutions (MIIs) | Stock exchanges, clearing corporations, depositories | Highest — most controls mandatory |
| Qualified Regulated Entities | Large stockbrokers, Qualified Stock Brokers (QSBs), large REs above defined thresholds | High — near-MII requirements |
| Mid-size Regulated Entities | Entities with moderate client base, AUM, or trading volume | Medium — most controls with some flexibility |
| Small-size Regulated Entities | Smaller brokers, smaller REs below mid-size thresholds | Lighter requirements, annual audits |
| Self-Certification REs | Entities with minimal systemic impact | Lightest — VAPT + self-certification |
Your category determines your audit frequency, SOC obligations, CISO reporting structure, whether ISO 27001 is mandatory, and your CCI (Cyber Capability Index) assessment method. Getting your categorization right is the first thing to do — and SEBI revised the categorization thresholds in April 2025, so entities that previously assumed a lower tier should recheck.
Note: Standalone Investment Advisers (IAs) and Research Analysts (RAs) registered only in those capacities were exempted from CSCRF compliance in the April 2025 revision. If you hold dual registrations, check your applicable category carefully.
What CSCRF Actually Mandates: The Key Requirements
Here is where most organizations lose the thread. CSCRF does not just ask you to have "good cybersecurity." It mandates specific, verifiable controls — with evidence submission timelines, auditor requirements, and reporting formats. These are the requirements that matter most:
1. Security Operations Center (SOC)
All REs must establish SOC capabilities for real-time security monitoring. The specifics depend on your category:
| Category | SOC Requirement |
|---|---|
| MIIs | Dedicated in-house or group SOC. Mandatory. No exceptions. |
| Qualified REs | Own SOC or group-level SOC. Mandatory. |
| Mid-size REs | May use the Market SOC operated by NSE or BSE as an alternative |
| Small-size / Self-Cert REs | Market SOC or minimal internal capability acceptable |
The Market SOC (M-SOC) operated by exchanges is specifically designed for smaller REs that cannot sustain a full in-house operation. Opting in does not eliminate compliance — you still need to ensure coverage aligns with CSCRF requirements.
MIIs and Qualified REs must also build dashboards integrated with log aggregators for automated compliance reporting. Manual SOC operations are increasingly insufficient for these tiers.
2. CISO Reporting Structure
For MIIs and Qualified REs, the CISO's role must be at least equivalent in level and standing to the CTO or CIO, and the CISO must report directly to the MD or CEO. This is a governance requirement with audit-visible implications — it needs to be reflected in org charts and board-approved governance documents.
Smaller REs without a dedicated CISO must assign clear accountability to a designated officer at an appropriate level.
3. ISO 27001 Certification
Mandatory for MIIs and Qualified REs. The certification scope must include the Primary Data Center, Disaster Recovery site, Near-DR site, SOC, and any colocation facility. Evidence of certification must be submitted along with the cyber audit report.
For Mid-size, Small-size, and Self-Certification REs, ISO 27001 is optional but recommended.
4. Vulnerability Assessment and Penetration Testing (VAPT)
VAPT is mandatory for all REs — but frequency and submission timelines differ:
| Category | VAPT Frequency |
|---|---|
| MIIs and Qualified REs | Half-yearly |
| Qualified Stock Brokers (QSBs) | Half-yearly, regardless of broader category |
| Mid-size REs with IBT or Algo trading | Half-yearly |
| Small-size REs with IBT or Algo trading | Half-yearly |
| All other REs | Annual |
| Self-Certification REs | Annual VAPT + self-certification |
VAPT must be conducted by CERT-In empanelled IS auditing organizations. The same auditing organization cannot conduct VAPT for more than three consecutive years — after that, a two-year cooling-off period applies before re-engagement.
High-severity vulnerabilities from non-implementation of patches must be closed within one week. All other findings must be closed within three months of VAPT report submission. Open findings after three months require CISO sign-off and must be closed before the next cycle.
VAPT is also mandatory after every major system release — not just on a periodic calendar basis.
5. Cyber Audit
Separate from VAPT, the full cyber audit verifies compliance with the entire CSCRF framework:
| Category | Audit Frequency | Scope |
|---|---|---|
| MIIs | Twice a year | 100% of critical systems + 25% sample of non-critical |
| Qualified REs | Twice a year | 100% of critical systems + 25% sample of non-critical |
| Mid-size REs with IBT/Algo | Twice a year | As above |
| Small-size REs with IBT/Algo | Twice a year | As above |
| All other REs | Once a year | As above |
| Self-Certification REs | Exempt from periodic cyber audit | VAPT only |
Audit reports must be submitted within one month of completion, accompanied by an MD/CEO declaration. Findings must be closed within three months. A follow-on audit to verify closure must be completed within six months of the initial audit. Any findings still open after six months require IT Committee approval.
Auditors must be CERT-In empanelled, with a minimum of three years of BFSI IT audit experience. CISA, CISM, CISSP, and GSNA are the recognized certifications for audit personnel.
6. IT Committee
Mandatory for MIIs, Qualified REs, and Mid-size REs. The IT Committee must include at least one independent external cybersecurity expert and must conduct periodic reviews of cybersecurity policies, incidents, and CSCRF compliance — with recommendations escalated to the Board.
For Small-size and Self-Certification REs, a formal IT Committee is not mandatory, but an IT expert's involvement and MD/CEO-level review is expected.
7. Incident Response and Reporting
All REs must maintain a Cyber Crisis Management Plan (CCMP) covering response scenarios, escalation paths, and recovery procedures. Incidents must be reported through SEBI's incident reporting portal within prescribed timelines.
For high-severity incidents, Root Cause Analysis and forensic investigations are mandatory. For low and medium severity incidents, forensic reports are required if the RCA is inconclusive or if SEBI/HPSC-CS specifically directs it.
8. Third-Party and Vendor Risk Management
All third-party vendors — including cloud service providers — must be covered under NDAs with explicit certification that they comply with CSCRF requirements. Periodic SEBI reports must highlight critical third-party activities.
For cloud adoption specifically:
- Data storage and processing must be in MeitY-empanelled data centers with valid STQC certification
- Encryption keys and key management operations must remain within India's legal boundaries
- Routing through foreign jurisdictions is a data sovereignty violation under CSCRF
- Cloud providers must maintain contractual back-to-back compliance from all subcontractors
9. Red Teaming and Threat Hunting
Mandatory for MIIs and Qualified REs. Goal-based adversarial simulation exercises (red teaming) must be conducted periodically to identify real-world weaknesses. Ongoing threat hunting and compromise assessment is also required for these tiers.
10. Post-Quantum Risk Assessment
CSCRF explicitly addresses post-quantum cryptography risk. All REs must include post-quantum threat scenarios in their periodic risk assessments. Cryptographic asset inventories must be maintained in preparation for Post-Quantum Cryptography migration timelines.
Compliance Timeline: Where Things Stand
| Milestone | Date |
|---|---|
| CSCRF issued | August 20, 2024 |
| Clarification circular issued | December 31, 2024 |
| MIIs, KRAs, QRTAs compliance | January 1, 2025 |
| Extended deadline for all other REs | August 31, 2025 |
| Zero Trust expectations clarified; critical systems definition expanded | August 28, 2025 |
| Comprehensive FAQ published (76 questions) | June 11, 2025 |
| VAPT report submission for FY 2025-26 (Self-Cert REs) | July 30, 2026 |
As of March 2026, the primary implementation deadline has passed for all entity categories. The focus has shifted from "when do we need to comply" to "are we actually audit-ready and can we demonstrate it."
Where Most BFSI Organizations Are Falling Short
Having worked across securities market intermediaries, AMCs, and broker-dealer operations, the gaps we consistently see are not in awareness of CSCRF — they are in execution depth. Here is where organizations are struggling the most:
SOC Coverage Without SIEM Depth
Many mid-size REs have signed up with managed SOC providers or the Market SOC but have not done the work to ensure their log sources are actually feeding the SOC meaningfully. A SOC contract is not the same as SOC coverage. If your SIEM is not ingesting identity logs, privileged account activity, and application-layer events — you have a coverage gap that will surface in audit.
VAPT That Doesn't Drive Closure
VAPT is being treated as a checkbox exercise. Reports are submitted, findings are logged — and then the closure follow-through breaks down. The one-week SLA for high-severity patch findings is routinely missed. Organizations need to integrate VAPT findings into their change management and patch management workflows, not manage them as a separate compliance track.
CISO Governance on Paper Only
For Qualified REs specifically, the CISO reporting-line requirement is frequently handled on paper without real structural change. If your CISO is functionally buried under IT operations and the board sees a CISO-to-MD reporting line on an org chart that does not reflect reality, this will not pass scrutiny in an audit.
Weak Third-Party Controls
Cloud migration has happened faster than third-party governance frameworks have kept pace. Many REs have STQC-certified primary infrastructure but non-compliant subcontractor exposure they are unaware of. The MeitY-empanelled CSP requirement extends to all subcontractors in the chain — not just the primary vendor.
No Documented Cyber Crisis Management Plan
The CCMP is a mandatory document. We regularly encounter organizations where incident response exists as institutional knowledge among a small IT team rather than a documented, tested, board-approved plan. Without documentation, there is no audit evidence.
Talk to our team about a CSCRF readiness assessment
CSCRF Compliance Roadmap: A Practical Approach
Phase 1: Categorize and Gap Assess (Weeks 1 to 3)
- Confirm your RE category under the April 2025 revised thresholds
- Map CSCRF requirements applicable to your category
- Conduct a structured gap analysis against current controls, documentation, and processes
- Identify CERT-In empanelled auditors and initiate engagement discussions
Phase 2: Governance and Structure (Weeks 3 to 6)
- Formalize CISO reporting structure with board-approved documentation
- Constitute or re-charter the IT Committee with an independent external expert
- Draft or update the Cyber Security Policy, IT Security Policy, and Cyber Crisis Management Plan
- Establish or validate third-party vendor risk registers and CSCRF compliance clauses
Phase 3: Technical Controls (Weeks 4 to 10)
| Control Area | What Needs to Happen |
|---|---|
| SOC / SIEM | Validate log source coverage; tune detection rules for identity and application events |
| IAM / PAM | Ensure privileged account monitoring feeds into SIEM; access certification in place |
| VAPT | Schedule CERT-In empanelled assessment; integrate findings into patch management workflow |
| Endpoint and Network | Patch management SLAs enforced; network segmentation documented |
| Data Protection | Encryption key management verified as India-resident; database activity monitoring active |
| Cloud | Validate MeitY empanelment + STQC certification for all CSPs and their subcontractors |
Phase 4: Audit Readiness (Weeks 8 to 12)
- Conduct internal dry-run against CSCRF auditor checklist (included in the framework's annexures)
- Ensure evidence is compiled: VAPT reports, closure evidence, ISO 27001 certificate, IT Committee minutes, CISO governance documents, CCMP
- Prepare standardized SEBI reporting formats for post-audit submission
- Engage CERT-In empanelled auditor for formal audit cycle
Phase 5: Steady State (Ongoing)
- Monthly: SOC performance review, open findings tracking
- Quarterly: IT Committee meeting, third-party risk review
- Half-yearly: VAPT cycle (for MIIs, Qualified REs, QSBs, and IBT/Algo REs)
- Annually: Full cyber audit, ISO 27001 surveillance, CCI self-assessment (Qualified REs), employee cybersecurity training
- Continuously: Threat intelligence integration, post-quantum risk monitoring
FAQ
My organization falls under both SEBI and RBI regulation. Which framework applies?
Both. CSCRF applies to your SEBI-regulated activities and infrastructure. RBI's cybersecurity frameworks (DCRR, NBFC guidelines, etc.) apply to your RBI-regulated activities. Where systems are interconnected, the audit scope under CSCRF must include those connected systems. SEBI has clarified that the CISO reporting structure under CSCRF takes precedence for SEBI-regulated functions, even if the RBI framework allows CISO reporting to an ED rather than MD/CEO.
We are a small broker. Do we need a full SOC?
Not an in-house one. Small-size REs can leverage the Market SOC operated by NSE or BSE. However, you cannot opt out of SOC-based monitoring entirely — the Market SOC subscription and active log source integration are expected. Self-Certification REs have the lightest requirement but are still expected to have minimal monitoring capability.
Can we use the same CERT-In empanelled firm for both VAPT and cyber audit?
Yes, the same firm can conduct both, subject to the three-year consecutive tenure rule. After three years with the same firm, a two-year cooling-off period applies before re-engagement. During the cooling-off period you must engage a different CERT-In empanelled organization.
What happens if we miss the VAPT submission deadline?
Non-compliance with CSCRF — including missed VAPT deadlines — can result in regulatory action by SEBI, potential suspension of operations, and reputational damage. SEBI has the authority to take enforcement action. Given that multiple deadline extensions have already been granted, regulators are unlikely to show continued leniency.
We use AWS or Azure for our workloads. Is that a problem?
Only if your cloud provider and its subcontractors are MeitY-empanelled with valid STQC certification, and if all data processing and encryption key management happens within India. Major CSPs operate STQC-compliant regions in India, but you need to contractually verify that subcontractors in the delivery chain are also compliant. Routing through a foreign jurisdiction — even transiently — creates a data sovereignty issue under CSCRF.
Does CSCRF require quantum-resistant cryptography right now?
Not immediately, but it requires you to assess the risk and maintain a cryptographic asset inventory in preparation for migration. The framework acknowledges post-quantum threats including "harvest now, decrypt later" attack vectors and mandates ongoing risk assessment. Organizations should be building awareness of their cryptographic dependencies now.
How do we handle an incident that occurs at 3 AM?
Your CCMP must define escalation procedures, including out-of-hours contact protocols. For Qualified REs and MIIs, the SOC operates 24/7 and has documented escalation paths. For smaller REs using the Market SOC, confirm what the escalation handoff looks like and whether you have a designated incident coordinator reachable outside business hours. SEBI's incident reporting portal requires timely submission — your incident response plan cannot have a "wait until morning" step.
SEBI CSCRF Compliance Consulting
Cyberaube Technologies works with SEBI-regulated entities on CSCRF gap assessments, SOC log coverage, PAM implementation, and VAPT remediation. Our cybersecurity compliance consulting services are built around the core technical pillars of CSCRF — SIEM, IAM, PAM, and database security.
Explore our compliance consulting services or schedule a CSCRF readiness assessment.
Conclusion
SEBI CSCRF is the most comprehensive cybersecurity mandate India's securities sector has ever faced. The deadline extensions are over. Audit cycles are running. For BFSI organizations that are still treating CSCRF as a future priority, the window for a relaxed implementation approach has closed.
The good news is that CSCRF is well-designed. It is not arbitrary regulation — it maps to real risk reduction. Organizations that implement it seriously will have meaningfully stronger security postures, not just compliant paperwork. The challenge is in execution: translating 300+ pages of framework into a working compliance programme without the specialised talent to do it internally.
At Cyberaube, we work with SEBI-regulated entities on exactly this problem. Our team brings deep platform expertise across SIEM (QRadar, Splunk), IAM and PAM (CyberArk, Okta, SailPoint), and database security (IBM Guardium) — the core technical pillars of CSCRF compliance. Whether you need a CSCRF gap assessment, help building your SOC log coverage, PAM implementation, or VAPT remediation support, we can help.
Schedule a CSCRF readiness consultation with our team
About the Author
Saurabh Pande is Co-Founder of Cyberaube Technologies with 13+ years of experience across enterprise security platforms including IBM Security, CyberArk, and QRadar. He has interviewed and placed 2,500+ cybersecurity professionals across SIEM, PAM, and IAM disciplines, and advises BFSI organizations on security operations strategy and compliance readiness.