IBM Guardium Database Security: Implementation Roadmap for Indian Enterprises (2026 Edition)
A fact-based guide to implementing IBM Guardium v12.2.1 for database activity monitoring and compliance in Indian enterprises. Covers verified architecture, deployment phases, and regulatory requirements.
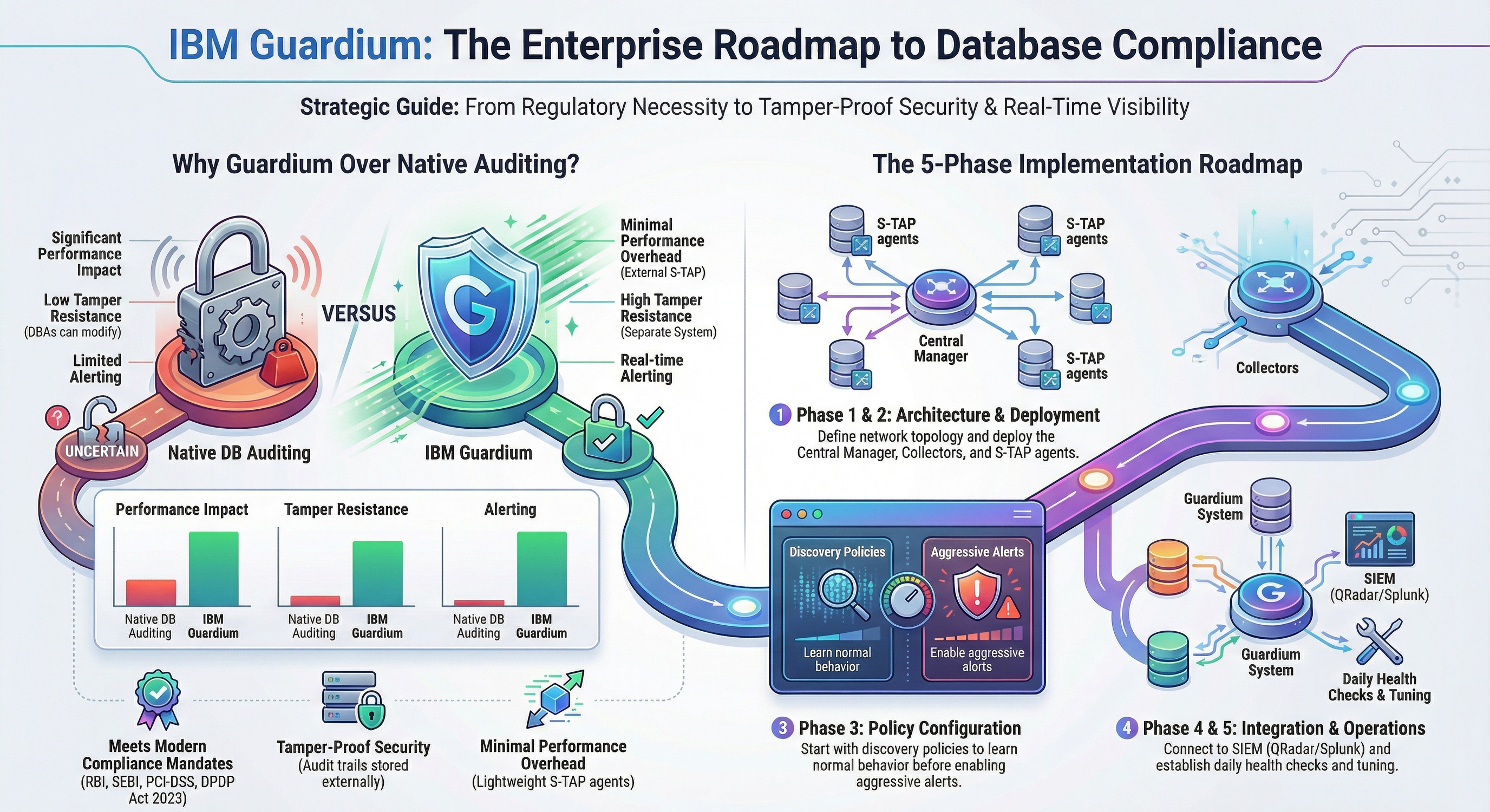
Executive Summary
IBM Guardium Data Protection v12.2.1 is the current enterprise-standard database activity monitoring (DAM) solution for regulated Indian organizations. As of 2025, SEBI's Cybersecurity and Cyber Resilience Framework (CSCRF) explicitly requires Database Activity Monitoring capabilities for regulated entities, with a Recovery Point Objective (RPO) of 15 minutes for audit data SEBI CSCRF FAQs, 2025.
For organizations facing RBI IT Governance mandates, SEBI CSCRF requirements, and DPDP Act 2025 obligations, database-level monitoring has shifted from best practice to regulatory mandate. DPDP Act 2025 requires Significant Data Fiduciaries to undertake annual audits and Data Protection Impact Assessments DPDP Rules 2025, Section 24.
This roadmap provides verified implementation guidance based on IBM's latest documentation and current Indian regulatory requirements.
Schedule a Guardium Implementation Consultation
Current Regulatory Landscape (2025)
SEBI CSCRF Requirements
SEBI's Cybersecurity and Cyber Resilience Framework mandates:
- Database Activity Monitoring (DAM) explicitly required for market infrastructure institutions SEBI CSCRF FAQs, 2025
- 15-minute RPO for audit data recovery
- Real-time alerting on policy violations and anomalies Cockroach Labs analysis
RBI IT Governance Mandates
RBI Master Directions require:
- Information asset classification based on confidentiality, integrity, and availability
- Monitoring of end-of-support dates for software and hardware
- Technology refresh plans for obsolete systems HewardMills analysis, 2024
- Database monitoring falls under "critical systems" classification
DPDP Act 2025 Audit Obligations
DPDP Rules 2025 mandate:
- Annual audits for Significant Data Fiduciaries
- Data Protection Impact Assessments (DPIA) every 12 months
- Independent data auditor appointments
- Ongoing monitoring and governance reviews DPDP Rules 2025, Section 24
IBM Guardium Data Protection v12.2.1
Current Version & Support
- Latest Version: 12.2.1 (released 2025)
- Supported Platforms: Documented in IBM Support Pages 7255260
- Upgrade Cycle: Major versions annually; support lifecycle 2-3 years
Supported Databases (2025)
Based on IBM Guardium 12.2.1 documentation:
Relational Databases:
- Oracle (all supported versions)
- Microsoft SQL Server (including 2022)
- PostgreSQL
- MySQL
- IBM Db2
- SAP Sybase
- Teradata
NoSQL & Cloud:
- MongoDB
- Apache Cassandra
- Elasticsearch (8.6.0+)
- Couchbase Server (7.1+)
- Amazon RDS (AWS)
- Azure SQL Database
- Google Cloud SQL
Mainframe:
- Db2 z/OS
- IMS
- VSAM
Full List: IBM Guardium Supported Data Sources
Pricing & Licensing (2025)
IBM Guardium offers two licensing models Gartner Peer Insights, 2025:
1. Subscription Model:
- Annual subscription based on number of monitored data sources
- Includes maintenance and support
- Cloud deployment options available
2. Perpetual Model:
- One-time license purchase
- Annual maintenance fees separate
- Traditional on-premises deployment
Pricing Factors:
- Number of database instances monitored
- Deployment model (on-prem vs cloud)
- Required capacity and usage
- Average enterprise cost: High TCO due to licensing and implementation complexity G2 Reviews, 2025
Implementation Architecture
Core Components
IBM Guardium's architecture uses a distributed model for scalability IBM Knowledge Center, 2019:
| Component | Function | Typical Deployment Ratio |
|---|---|---|
| Central Manager | Policy management, reporting, administration | 1 per enterprise |
| Collector | Database traffic capture and analysis | Based on PVUs/VUs and audit mode [IBM Sizing Guide, 2025] |
| Aggregator | Consolidation from multiple collectors | 1 per 8 collectors [IBM Guardium V10.0 Technical Requirements, 2015] |
| STAP (S-TAP) | Lightweight agent on database servers | 1 per database server |
| GIM Server | STAP deployment and update management | 1 per environment |
Important: Collector sizing is based on Processor Value Units (PVUs) or Value Units (VUs), database activity volume, and audit mode - not simply database count. The "1 per data center or 1 per 50 databases" oversimplification does not account for these critical factors [IBM Guardium V10.0 Technical Requirements, 2015]. See the Sizing section below for detailed guidance based on IBM's official documentation.
Collector Sizing Guidelines
Collector deployment depends on multiple variables, not a simple database count ratio. According to IBM Guardium V10.0 Technical Requirements, sizing is determined by:
Primary Sizing Factors:
- Processor Value Units (PVUs) or Value Units (VUs): The licensed capacity of monitored databases
- Audit Mode: Different audit modes consume collector resources at different rates
- Database Activity Volume: Peak query volume and transaction rates
- Hardware Specification: Collector appliance CPU, memory, and disk I/O capacity
IBM's Sizing Table (per collector):
- Comprehensive Audit Mode: 4000 PVUs per collector
- Sensitive Objects Audit Mode: 8000 PVUs per collector
- Privileged Users (Windows): 8000 PVUs per collector
- Privileged Users (Unix): 12000 PVUs per collector
Example Calculation: Monitoring Oracle databases on 17000 PVUs with Sensitive Objects auditing requires three collectors (roundup of 17000/8000 = 3) [IBM Guardium V10.0 Technical Requirements, 2015].
Additional Considerations:
- Virtual Environments: Add at least 50% more collectors due to VMware parallel processing limitations
- Data-Level Access Control (S-GATE): Add at least 50% more collectors to guarantee minimal latency
- Non-Standard Hardware: Adjust sizing metrics based on performance differences from standard IBM x3550 M4 appliances
- Audit Data Retention: Longer retention periods require additional disk capacity and may impact collector performance
Key Takeaway: Collector deployment must be based on PVU/VU calculations, activity volume analysis, and audit mode requirements. The simplified "50 databases per collector" rule ignores these critical sizing factors and can lead to inadequate capacity [IBM Guardium V10.0 Technical Requirements, 2015].
Network Architecture Options
Agent-Based (STAP):
- Captures all database activity including local connections
- Lightweight performance impact (<5% CPU overhead)
- Requires installation on database servers
Network-Based (Agentless):
- Uses SPAN/TAP ports to capture network traffic
- No software installation on database servers
- May miss local database connections
Deployment Models 51Security, 2019:
- Central Manager as GIM Server
- Aggregator as GIM Server
- Collector as GIM Server
- Dedicated GIM appliance
Network Requirements
Plan for significant internal traffic:
- STAP to Collector: Encrypted database activity streams
- Collector to Aggregator: Aggregated security events
- Collector to Central Manager: Policy updates and configuration
- Typical bandwidth: 10-50 Mbps per 100 databases
Implementation Roadmap (Verified Timelines)
Phase 1: Discovery & Architecture (2-3 weeks)
Activities:
- Document all database types, versions, and connection methods
- Map network topology and identify collector placement
- Assess current database auditing and logging practices
- Identify compliance gaps (SEBI, RBI, DPDP)
Deliverables:
- Database inventory with classification (critical, sensitive, regulated)
- Network architecture diagram
- Compliance gap analysis
- Hardware sizing requirements
Common Finding: Most organizations lack complete database inventory, especially cloud databases .
Phase 2: Infrastructure Deployment (4-6 weeks)
Week 1-2: Core Infrastructure
- Deploy Central Manager (primary and standby)
- Deploy initial Collector(s)
- Configure Aggregator (if required)
- Establish GIM Server
Week 3-4: STAP Deployment
- Install STAP agents on pilot databases (2-3 non-production)
- Configure network inspection points (if agentless)
- Validate data flow and connectivity
Week 5-6: Initial Tuning
- Verify database traffic capture
- Test alert delivery
- Establish baseline performance metrics
Critical Success Factor: Start with non-production databases to validate architecture before production deployment.
Phase 3: Policy Configuration (2-4 weeks)
Week 1: Learning Mode
- Enable discovery policies to understand normal behavior
- No alerting - pure observation
- Document baseline activity patterns
Week 2: Basic Monitoring
- Enable alerts for:
- Failed login attempts
- Privilege escalation
- Schema changes (DDL)
- After-hours access
Week 3: Data Classification
- Identify sensitive data (PAN, PII, health records)
- Map sensitive tables/columns
- Create data classification policies
Week 4: Advanced Policies
- Implement access pattern analysis
- Enable anomaly detection
- Configure custom policies for business logic
Policy Priority Order [IBM Best Practices]:
- Privileged user monitoring (DBAs)
- Sensitive data access
- Schema and configuration changes
- Bulk data extraction
- Anomalous access patterns
Phase 4: Integration & Automation (2-3 weeks)
SIEM Integration:
- Forward alerts to QRadar, Splunk, or ArcSight
- Configure alert correlation
- Set up compliance dashboards
Ticketing Integration:
- Auto-generate tickets for policy violations
- Integrate with ServiceNow or Jira
- Configure escalation workflows
Identity Integration:
- Correlate database activity with IAM systems
- Link OS users to database accounts
- Monitor privileged access management (PAM) integration
Phase 5: Production Rollout (Ongoing)
Phased Approach:
- Wave 1: Non-production databases (Week 1-2)
- Wave 2: Low-risk production databases (Week 3-4)
- Wave 3: Critical production databases (Week 5-8)
- Wave 4: Mainframe and specialized databases (Week 9-12)
Typical Timeline: Full enterprise deployment takes 12-16 weeks for organizations with 50-200 databases.
Get Help Planning Your Guardium Rollout
Common Implementation Pitfalls (Verified)
Pitfall 1: Over-Monitoring from Day One
Problem: Enabling aggressive policies immediately generates thousands of daily alerts Impact: Alert fatigue, ignored violations, operational disruption Solution: Start with 2-4 weeks of learning mode; enable alerting gradually
Pitfall 2: Network Architecture Gaps
Problem: STAPs cannot reach collectors due to firewall rules or network segmentation Impact: Data loss, incomplete monitoring, false sense of security Solution: Document network paths before deployment; open required ports (16000-16100)
Pitfall 3: Inadequate Infrastructure Sizing
Problem: Collectors cannot handle peak traffic volumes Impact: Data loss, performance degradation, alert delays Solution: Size for peak load + 30% headroom; monitor disk, CPU, network continuously
Pitfall 4: "Set and Forget" Mindset
Problem: Initial policies become stale; reports go unread; system health degrades Impact: Compliance gaps, missed incidents, failed audits Solution:
- Monthly policy reviews and tuning
- Weekly health checks (system performance, disk space, connectivity)
- Quarterly compliance report reviews
- Annual architecture review
Pitfall 5: Underestimating Skill Requirements
Problem: Teams lack Guardium expertise for implementation and operations Impact: Delayed deployment, misconfigured policies, operational errors Solution:
- Start with external implementation support
- Develop internal administrators over 6-12 months
- Retain external experts for upgrades and complex issues
- Invest in IBM training and certification
Discuss Your Guardium Implementation Challenges
Compliance Mapping
SEBI CSCRF Compliance
| CSCRF Requirement | Guardium Capability |
|---|---|
| Database Activity Monitoring (DAM) | Core STAP/Collector architecture |
| 15-minute RPO | Real-time data collection and replication |
| Audit logging and monitoring | Tamper-proof audit trails, policy violation alerts |
| Real-time anomaly detection | Advanced analytics and ML-based detection |
RBI IT Governance Compliance
| RBI Mandate | Guardium Implementation |
|---|---|
| Information asset classification | Data classification policies and reporting |
| Critical system monitoring | Priority alerting for critical databases |
| End-of-support monitoring | Inventory tracking and compliance reports |
| Technology refresh planning | Database version and patch reporting |
DPDP Act 2025 Compliance
| DPDP Requirement | Guardium Feature |
|---|---|
| Personal data access audit | Complete audit trail of all data access |
| Data Protection Impact Assessment | Pre-implementation and ongoing activity analysis |
| Annual independent audits | Exportable compliance reports and logs |
| Significant Data Fiduciary monitoring | Real-time alerting on sensitive data access |
Discuss Your Compliance Requirements
Operations & Maintenance
Daily Operations
- Review exception reports (failed collection, connectivity issues)
- Monitor system health dashboards
- Respond to critical alerts within SLA
Weekly Tasks
- Health check: Disk space, CPU, memory utilization
- Alert volume analysis and false positive tuning
- Policy effectiveness review
Monthly Activities
- Compliance report generation (PCI-DSS, RBI, SEBI)
- Policy tuning based on business changes
- User access review
- Capacity planning analysis
Quarterly Reviews
- Architecture review and optimization
- Upgrade planning (Guardium patches and versions)
- Compliance audit preparation
- Executive dashboard updates
Annual Activities
- Full compliance audit
- Disaster recovery testing
- Technology refresh assessment
- Budget planning for expansion
Staffing Requirements
Implementation Team
| Role | FTE | Duration |
|---|---|---|
| Project Manager | 0.25 | 6 months |
| Guardium Architect | 0.5 | 3 months |
| Database SME | 0.5 | 4 months |
| Network Engineer | 0.25 | 2 months |
| Compliance Analyst | 0.25 | 3 months |
Operations Team (Post-Implementation)
| Role | FTE | Responsibilities |
|---|---|---|
| Guardium Administrator | 0.5 - 1.0 | Daily operations, policy tuning, user management |
| Security Analyst | 0.5 - 1.0 | Alert triage, incident investigation, reporting |
| Database SME | 0.25 | Technical advisory, policy validation |
| Compliance Officer | 0.25 | Audit support, compliance reporting |
Skill Development Timeline:
- Months 1-3: External support for implementation
- Months 4-6: Shadow operations with external mentor
- Months 7-12: Independent operations with periodic external review
- Month 12+: Fully independent with external support for upgrades/complex issues
ROI & Business Justification
Cost Components
- Software Licensing: Subscription or perpetual (based on database count)
- Infrastructure: Hardware/appliances or cloud resources
- Implementation: External consulting (typical range: $200K-$500K for enterprise)
- Operations: FTE costs for administration and analysis
- Training: IBM certification and ongoing skill development
Benefit Categories
- Compliance Avoidance: Penalty avoidance (RBI, SEBI fines ₹5 crore+ possible)
- Breach Risk Reduction: Database breaches average ₹4,000 per record in India
- Audit Efficiency: Automated compliance reporting vs. manual evidence collection
- Operational Efficiency: Centralized monitoring vs. native database auditing
- Incident Response: Faster detection and investigation of database incidents
Typical ROI Timeline
- Year 1: Negative ROI (implementation costs)
- Year 2: Breakeven or positive ROI (depending on compliance penalties avoided)
- Year 3+: Strong positive ROI, especially for organizations with compliance issues or breach history
Break-even Point: Typically 18-24 months for regulated enterprises with 50+ databases
Next Steps & Resources
Immediate Actions
- Download IBM Guardium documentation: IBM Support Pages
- Review regulatory requirements:
- Conduct database inventory: Document all databases with classification
- Assess compliance gaps: Map current state to regulatory requirements
Professional Services
Cyberaube Technologies provides IBM Guardium implementation and managed support services:
- Implementation planning and architecture design
- Infrastructure deployment and configuration
- Policy development and tuning
- Compliance reporting and audit support
- Managed services (24/7 monitoring and platform maintenance)
Training & Certification
- IBM Guardium Fundamentals (for administrators)
- IBM Guardium Advanced Implementation (for architects)
- IBM Guardium Compliance and Reporting (for analysts)
- Consider IBM Skills Gateway for ongoing skill development
Schedule a Guardium Consultation
IBM Guardium Implementation Services in India
Cyberaube Technologies specialises in IBM Guardium implementation and managed support for Indian enterprises navigating SEBI CSCRF, RBI IT Governance, and DPDP Act requirements. Our certified Guardium SMEs have deployed v12.x across BFSI, healthcare, and technology sectors.
View our professional services or schedule a Guardium consultation.
About the Author
Saurabh Pande is Co Founder of Cyberaube Technologies with 10+ years of hands on experience implementing IBM Guardium v12.x, database security programs, and DAM solutions for SEBI-regulated entities and RBI-governed banks.
About Cyberaube
Cyberaube provides cybersecurity staffing, 24/7 managed security services, and expert consulting for SIEM, IAM, and data protection platforms. Our certified specialists implement and operate QRadar, Splunk, ArcSight, CyberArk, Okta, SailPoint, and integrated security stacks for enterprises across India and globally.